Vendor Risk Management
63% of Breaches are a Result of Third Party Vendors.
VENDEFENSE is a best-in-class vendor risk management platform that is simplified, standardized, and entirely defensible when used to manage your third-party information security risk management program.
Vendor Risk Management Steps
1. Take Inventory of Your Vendors
Every vendor that your organization does business with must be included in the third-party inventory. It’s not that every vendor poses a significant risk; it’s that you must show your due diligence regardless.
- Import vendors one at a time or all at once
- Easily manage all vendor relationships
- Automated annual renewal of all vendors
- Scheduling of future renewals
- Managing all vendors keeps you defensible
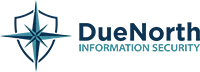
2. Classify Your Vendors
Next, begin to narrow your focus on the vendors who pose the most risk to your organization. You do this by classifying all vendors as high, medium or low risk. Risk is determined by their access to information and how critical that information is.
- Invite team members who have the relationship with the vendor
- Easily classify all vendors as high, medium or low risk
- Risk managers are notified when a classification is ready to review
- Classifications are customizable to meet your needs
- Increased defensibility: All vendors are managed and classified
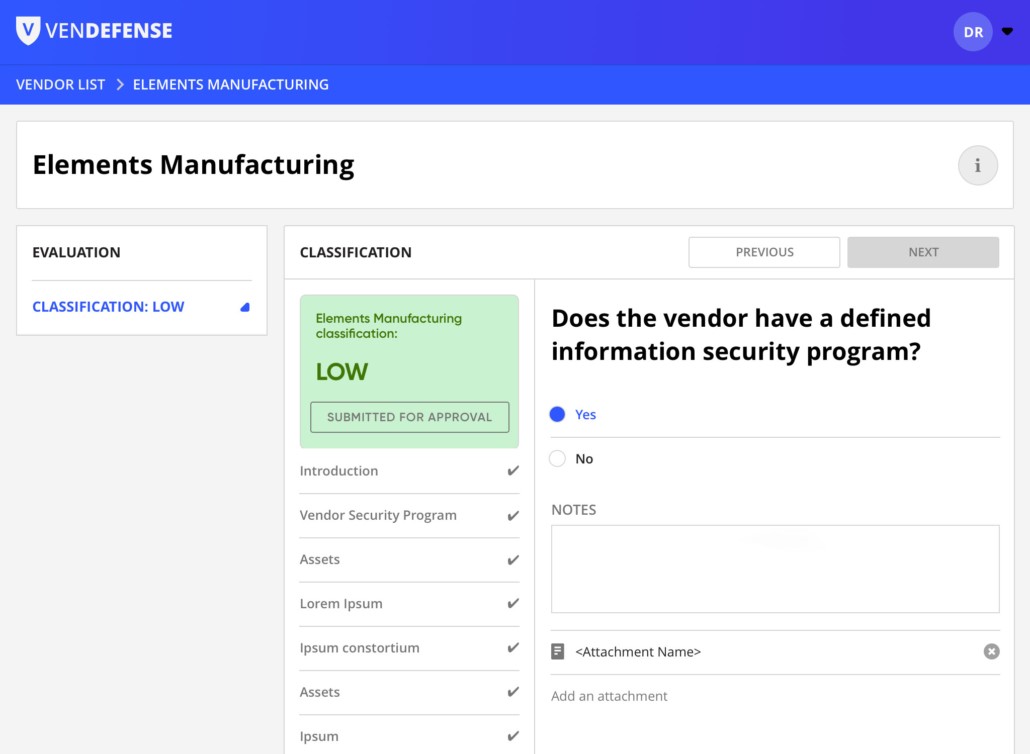
3. Assess Risk
Now that you know all the vendors’ potential impact, medium- and high-risk vendors must demonstrate what safeguards they have in place by completing a FISASCORE self-assessment. This will determine their residual risk, which is the remaining risk that must be addressed.
- Assessments are performed using the FISASCORE risk assessment
- FISASCORE is based on industry standards including ISO and NIST
- Assessments cover all areas of information security: administrative, physical and technical controls
- Built-in metrics allow you to focus on your riskiest vendors
- Easily see the FISASCOREs of all vendors in the dashboard
- Workflow engine manages all communications with your vendor
- Increased defensibility through standardized questions and objective responses
4. Set Thresholds
Some percentage of your vendors will pose an unacceptable information security risk to your organization. You won’t know what percentage, or what to do about it, without reaching this part of the process. You must establish objective thresholds for information security risk for vendors and treat them appropriately.
- Risk managers are notified when an assessment has been completed
- Easily review assessment results, including the areas where your vendors need improvement
- Select from one of four ways to treat your vendor: accept, remediate, transfer or avoid
- Workflow engine manages communicating remediation items
- Helps your vendors become more secure, which is good for them and for you
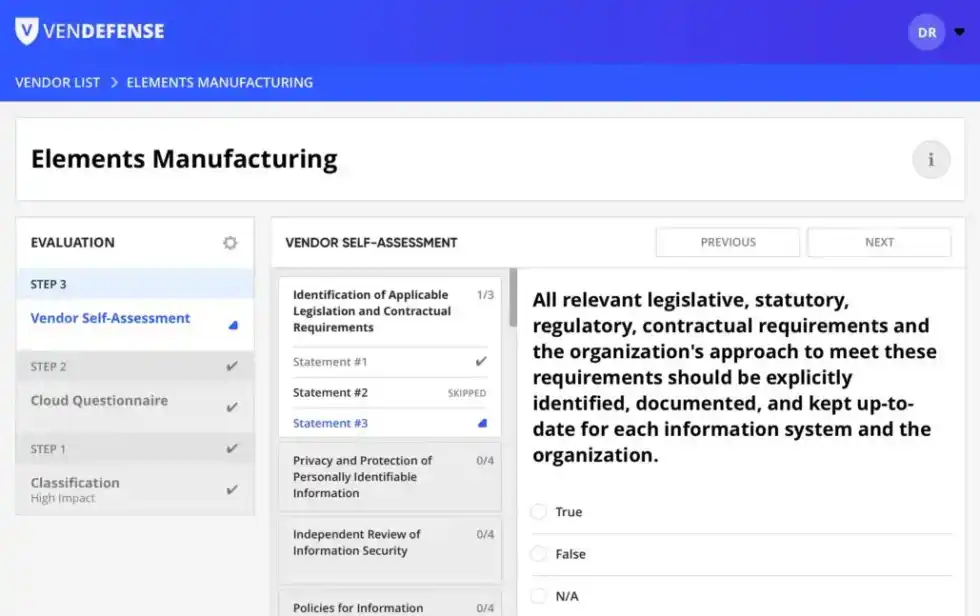
5. Assign Remediation
It’s not enough to just assess risk; risk must be processed and mitigated. For those vendors that you selected “Remediate,” VENDEFENSE automatically generates a remediation plan based on the low-scoring areas of their FISASCORE assessment. As vendors remediate vulnerabilities, their information security posture improves and so does their FISASCORE.
- A remediation plan is generated and sent to the vendor
- Risk managers can order an onsite, validated FISASCORE assessment
- You’re notified as vendors complete tasks in their remediation plan
- You control when you are willing to accept a vendor
- Managing risk of all vendors makes you defensible
6. Easily Visualize all Your Vendors
The power of VENDEFENSE lies in its intuitive dashboard that allows you to see all your vendors at once, identify the overall risk exposure of your organization, and pinpoint where in your organization the risk is coming from.
- View all vendors in one dashboard
- Easily see which vendors pose the greatest risk and which are scheduled for review
- View FISASCOREs for all your risky vendors and your company’s aggregate FISASCORE
- View FISASCORE trends over time
- Generate custom reports for management and the Board of Directors
Call Us

Let Us Know How We Can Help
Get More Information Today
"*" indicates required fields